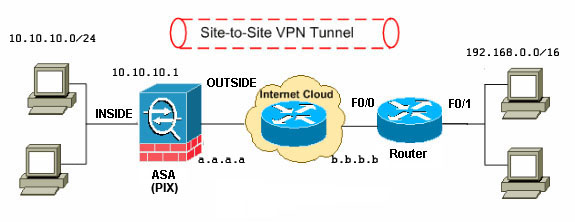
=== Cisco ASA config ===
enable password /pas/ encrypted
passwd /pas/ encrypted
!
interface Vlan1
nameif inside
security-level 100
ip address 10.10.10.1 255.255.255.0
!
interface Vlan2
nameif outside
security-level 0
ip address a.a.a.a 255.255.255.0
!
interface Ethernet0/0
switchport access vlan 2
!
interface Ethernet0/1
!
access-list 100 extended permit icmp any any
access-list inside_nat0_outbound_1 extended permit ip 10.10.10.0 255.255.255.0
192.168.0.0 255.255.0.0
!
access-list outside_1_cryptomap_1 extended permit ip 10.10.10.0 255.255.255.0
192.168.0.0 255.255.0.0
!
global (outside) 1 interface
nat (inside) 0 access-list inside_nat0_outbound_1
nat (inside) 1 10.10.10.0 255.255.255.0
access-group 100 in interface outside
route outside 0.0.0.0 0.0.0.0 a.a.a.x 1
!
crypto ipsec transform-set ASA_TR_SET esp-aes-256 esp-sha-hmac
crypto map outside_map 1 match address outside_1_cryptomap_1
crypto map outside_map 1 set peer b.b.b.b
crypto map outside_map 1 set transform-set ASA_TR_SET
crypto map outside_map interface outside
crypto isakmp enable outside
crypto isakmp policy 10
authentication pre-share
encryption aes-256
hash sha
group 2
lifetime 86400
!
aaa authentication ssh console LOCAL
!
ssh 0.0.0.0 0.0.0.0 outside
ssh timeout 10
!
username /user/ password /pas/ encrypted
!
tunnel-group b.b.b.b type ipsec-l2l
tunnel-group b.b.b.b ipsec-attributes
pre-shared-key *
!
=== Cisco Router Config ===
!
crypto isakmp policy 10
encr aes 256
authentication pre-share
group 2
!
crypto isakmp key /key/ address a.a.a.a no-xauth
!
crypto ipsec transform-set ASA-IPSEC esp-aes 256 esp-sha-hmac
!
crypto map ASAL2L_CLIENT 10 ipsec-isakmp
description Crypto map for ASA
set peer a.a.a.a
set transform-set ASA-IPSEC
match address 110
!
interface FastEthernet0/0
ip address b.b.b.b 255.255.255.0
crypto map ASAL2L_CLIENT
!
ip route 10.10.10.0 255.255.255.0 b.b.b.x
!
access-list 110 permit ip 192.168.0.0 0.0.255.255 10.10.10.0 0.0.0.255
!
При подключении программных Cisco VPN клиентов через Fa0/0, добавляем в конфиг на Cisco Router`е
username /username/ secret /password/
!
aaa new-model
!
aaa authentication login userauthen group local
aaa authorization network groupauthor local
!
crypto isakmp client configuration group
key /key/
dns x.x.x.x
wins x.x.x.x
domain domain.local
pool cisco_client_pool
acl 150
!
!
crypto ipsec transform-set CISCOCLIENT esp-aes 256 esp-sha-hmac
!
crypto dynamic-map CISCOCLIENT 10
description Dynmap for Soft Cisco VPN Client
set transform-set CISCOCLIENT
reverse-route
!
crypto map ASAL2L_CLIENT client authentication list userauthen
crypto map ASAL2L_CLIENT isakmp authorization list groupauthor
crypto map ASAL2L_CLIENT client configuration address respond
!
crypto map ASAL2L_CLIENT 65000 ipsec-isakmp dynamic CISCOCLIENT
!
ip local pool cisco_client_pool 192.168.x.x 192.168.x.z
!
access-list 150 permit ip x.x.0.0 0.0.255.255 any
!
|